- Hours after the US airstrike on Iranian territory, Iranian-backed hackers took down US President Donald Trump’s social media platform.
- Users were struggling to access Truth Social in the early morning following the alleged hack.
- As the US continues to insert itself into the ongoing Iran-Israel conflict, the US government believes more cyberattacks could happen.
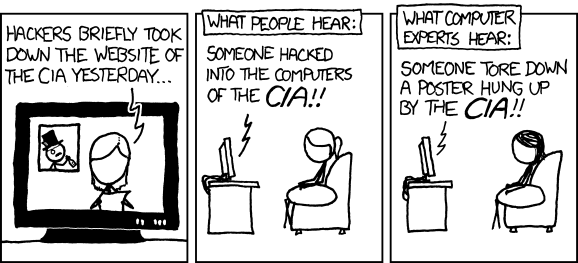
I mean it does depend on the extent of the hack. But usually taking down the website, they don’t take the databases or anything
source: https://xkcd.com/932/
(for those that want to read the alt-text)
Hacking a Social Media profile --> Tearing down a poster Hacking a Website --> defacing a facade
If the blinds arent closed by or a window is left open by accident, some information could get out. If the doors arent locked, the attacker could get access to further information.
They didn’t hack anything. Just your plain old DDoS attack which took the service offline for a while, nothing was (at least based on what I read) actually hacked (or cracked as old-school folks like me would like it to be called) or stolen.
Unclear from the article but, while a bit pedantic, this sounds more like it was potentially a DDoS attack rather than a proper “hack”.
In an age where “willfully giving out your account password” is called hacking, here I’d call it tomato or tomato.
Social Engineering is hacking cmv.
No, because I agree.
There’s usually an element of that with cracking passwords. Even if you just try and pick a good wordlist for a target you’re already engaging in a way. The more you know about them the shorter the wordlist. And if you spend enough time getting to know shit about them you can reduce the wordlist to one entry because they told you the password. In a way. It’s not necessarily a completely different process is my point.
You can argue it’s a classic ID-10T error in your workflow.
But nobody has discovered a security vulnerability within the system architecture. This is the system operating as designed, abet with the wrong person standing in front of the terminal.
That’s called a PICNIC - Problem In Chair Not In Computer.
PEBKAC
That’s cracking, not hacking. If you’re going to be pedantic, be correct.
However you want to phrase it, they’re very different problems with different solutions.
“Someone picked the lock on my door and got into my house” is meaningfully distinct from “Someone stole my keys”.
It was hacking according to Kevin Mitnick (RIP) so, it’s probably safe to say that your view doesn’t need to be changed.
here I’d call it tomato or tomato.
It’s pronounced tomato
Potato potato
You can keep your nasty chips
313 Team is an Arabic-interest hacker collective, aligned with Iran, Palestine and Iraq, they reportedly used a distributed denial of service (DDoS) attack against Truth Social.
The article seems pretty clear to me. Maybe it was updated?
In order to launch a meaningful DDoS there must be thousands of compromised machines to use. I would absolutely say compromising such a large amount of machines is hacking.
A lot of DDOS attacks nowadays are from a DDOS for hire service.
So there could be hacking done, or just a bitcoin transfer.
These DDOS for hire services make use of hacked machines as botnets to perform the DDOS attacks.
So while the people paying for the service didn’t hack anything, the people performing the DDOS certainly did.
Or they just found a buffer overflow bug on their border router/firewall. I can’t imagine Truth Social has a keen network engineering team keeping up to patching and vulnerabilities.
Doesn’t Truth Social run a super old custom modded version of Lemmy? That thing must have a ton of vulnerabilities.
It uses Mastodon (ActivityPub disabled), and Soapbox-FE.
It’s absolutely hacking those computer, just not the site. I just don’t want to get overly excited for something that doesn’t have much meat to it.
And nothing of value was lost.
Value gained, actually.
Less AI generated garbage.
Things of negative value were lost :D
It feels weird to be in support of the goals of an Iranian hacker group.
Its like watching two shitty people have an argument.
“let them fight.”
The only problem is that felon 47 isn’t going to fight. Innocent americans are going to get killed and that disgusting psychopath is going to spit on their graves.
Yeah it will indiscriminately hurt Iranians and Americans and not our rulers. We were both already suffering under our leaders before the American government decided to go to war with Iran.
I may need to go reread Jingo…
Innocent Americans don’t wear the US fascist army uniform.
I will spit on their grave.So let the downvoting, bootlicking and whitewashing begin.
You’ll have to be creative, not this tired garbage:

So the entirety of all branches are all responsible equally. Got it
Its a pretty childish take. Somehow my statement just wasn’t good enough. Not enough black and white. Too much grey.
“I didn’t personally bomb weddings or hospitals, I only made a cog for the missile” doesn’t excuse them.
So yes, they can all go to hell
He would have to even think about them to do that. I doubt the ground level costs of his actions and choices ever enter his mind in any real way.
Oh he thinks of them. He thinks of them as trash.
Problem?
How many innocent lives have been lost to US military action though out the world?
Collateral damage.
Talking about one thing but you want to talk about all the things.
They could revolt
They could sprout wings and fly to fairy land.
What innocent Americans are you talking about? If trade ships are attacked, maybe. If it’s military personnel, none of them are innocent as they are still “following orders”.
So everyone of us is guilty. Fuck you!
Don’t know why do you say “everyone”, I certainly didn’t say that. But if you are in the military of a country that is invading other country and continue to be in the military then you are definitely not innocent(though transferring to a different location might be a compromise).
Tankie fucktoid alert
What did Iran do? Seems like all the shitty is on one side.
Iran is known for its barbaric treatment of women who refuse the forced muslim dress code. They are a equally corrupt government. No good people involved at the upper levels. SSDD.
Yeah good thing the US respects women’s autonomy and isn’t being strangled by a fundamentalist religious movement that wants to force women to be nothing more than incubators, maids, and fuck toys…😒
Most of us do respect womens autonomy. I know I taught my daughter that. The loud mouth weaklings don’t. They hate that women don’t have to spread on command.
I couldnt give a single flying fuck if “most of you” are such good people that you’d willingly live in a militant feminist matriarchy; the fact is our enemy is not Iran or it’s people and you’re here patting yourself on the ass for having the literal minimum level of decency expected of a father
evangelical-christian-nationalists
Both of you are right but there’s definitely levels to how much worse it is in Iran
or Alabama
Different doesn’t necessarily equate to worse. The IR does oppress women, without a doubt; but American society exploits young women’s sexuality for financial gain, psychologically manipulates them into prohibitive gender norms that are impossible to achieve without vast amounts of wealth and privilege, and then tells them the most important thing they can aspire to be is mother to a man’s offspring.
In short, you, your society, and your government are not as different-and clearly not any better-from any other in the world.
A lot of this comment hinges on your belief that US women are not intelligent enough to to understand that exploitation and manipulation. Knowledge has progressed a lot in the last 20 years. Look at the under 18 and 20-24 age groups

There are much better examples of the subjugation of women in the US right now than to pin the societal oppression on US’ fostering of an anti intellectual society.
Iran has more FEMALE engineers than the US and less of it’s population in jail.
Iran’s healthcare has been rated excellent by UNICEF.
I could continue, but facts can’t win from the propaganda machine online.
So I’m just gonna laugh make fun of it.The freedom of both women and the general public is not solely dictated by healthcare and the ability to attain higher education.
Does a free society cut off country wide access to the external internet?
Iran is actively lying to its citizens saying they destroyed the US base in Qatar and there was minimal damage to Iranian nuclear facilities. Both outright lies. This is not a free golden society.
How many women are persecuted from laws around the head dressing and other clothing related issues.
Boiling womens rights down to they can become an engineer and have good healthcare is laughably pathetic and on the verge of being a conservative talking point I would hear on fox news in justification for stripping away more rights. Pinning the struggle of US women against Iranian women is an incredibly pathetic mindset that only fosters negativity.
Wait fr?
While there are religious extremists in Iran, their level of influence on Iranian culture is not anywhere near what you’re saying. You’re just repeating western propaganda.
They did have a controversial new dress code law that was supposed to go into effect at the end of last year, but it was blocked for being to extreme and vague.
However, my state just forced a brain dead woman to incubate a baby against the family’s will. So I’m inclined to agree with those saying the religious extremists exercise greater control in the US than Iran, and by your standards that means they should bomb us. Because I guess you think killing people is equal to freeing them.
You are stretching that one out. I don’t support Israel any more than I support Iran. They are both trash.
You’re repeating Israeli lies. So you’re either surreptitiously supporting Israel, or you’re serving as a useful idiot.
deleted by creator
Yeah the US/hasbara propaganda tools are out in full force.
Sure this cunt is one of them
SSDD? Same shit, different dictator - I like it
Solid-State Disk Drive, it’s a regular hard drive with the platters hot-glued to stay still
That’s right. The platters are heavy, and the reader head is light, so we just whip the reader head around at 7200rpm
It would get even worse if the regime fall. Just look at iraq, afghanistan, libya, syria
So if the US killed those women, problem solved? I don’t get your logic.
You try using logic. I didn’t say anything of the sort. You came up with that yourself.
LOL
The literal hasbara operative excuse to excuse them for genociding those misanthrophic barbarian Palestinians.
Really, you’re all so boring and unimaginative.
Must be tiring defending the many many warcrimes from USSA/pissrahell.
Glad you’re getting youe ass kicked and turning into Gaza yourself, it warms my heart.
“Hacker group”.
What a joke. Any kid with a credit card can unleash a ddos attack on a website.
An irrelevant website none the less. If that pile of shit goes down then the entire world benefits.
Not really. Most people around the world are pretty much in the same boat. The “leaders” of governments try to propagandize differences, but everyone is living the same shitty existence. Elites vs poors across the globe. Occasionally you get groups that are extremely radical, but it’s not specific really to any country (We see a lot of out of the ME and Africa mostly due to prolonged Colonial abuse, admittedly.)
I’m still at a loss for words thinking that any real human people joined truth social. We really failed as a species…
Equally upsetting. The site is truthsocial.com not truth.social
Someone should buy truth.social and make it redirect to something trump’s base hates.
Annoyingly, already registered
Meat spin?
They said something they hate.
…with a jump scare?
Like Wikipedia?
Really you should have it direct to a clone of the site, but with fake accounts pushing whatever agenda you want.
I’m thinking it might have some comedic value and if you’re trying to beat the stock market…
Fascists arent people. Antifa osint people joined to watch.
DDoS is not hacking
The word “hack” is pre-internet. A “hack” journalist or a “hack job” is basically something unprofessional. It is movies that turned “hackers” into someone that gained access to the “mainframe”. In the realm of computer systems, I would argue that a “hack” is doing anything the system was not intended/designed to do. A successful DoS or DDoS needs to find some component of the system that wasn’t designed to handle the amount of traffic about to be sent to it.
There are protections for DDoS (iptables, fail2ban, Cloudflare and so on), you have to figure out a way around them, that’s a hack.
The current tech-related usage was coined at MIT to mean working on a system. Funny that the oldest recorded source comes from MIT model railroad team.
Define hacking.
I’d start with the following, and refine if necessary:
“Gaining unauthorized access to a protected computer resource by technical means.”
- Port scanning --> Not hacking because there isn’t any access to resources gained*
- Using default passwords that weren’t changed --> Not hacking because the resource wasn’t protected*
- Sending spam --> Not hacking because there isn’t any access to resources gained
- Beating the admin with a wrench until he tells you the key --> Not hacking because it’s not by technical means.
- Accessing teacher SSN’s published on the state website in the HTML --> Not hacking because the resource wasn’t protected, and on the contrary was actively published**
- Distributed denial of service attack --> Not hacking because there isn’t any access to resources gained
* Those first two actually happened in 2001 here in Switzerland when the WEF visitors list was on a database server with default password, they had to let a guy (David S.) go free
** The governor and his idiot troupe eventually stopped their grandstanding and didn’t file charges against Josh Renaud of the St. Louis Post-Dispatch reporter, luckilyOh man.
My comment was intended to imply that the term “hacking” defies definition because it has been grossly overused and misconstrued over many decades.
Sure you might be able to convey what it means to you but of course it means different things to everyone else, with each definition being equally appropriate.
Er go, any discussion is one of semantics.
You know my first instinct wast to reply with: “No.”
Maybe I should have stuck with that. I had a feeling this would lead nowhere.
I had a feeling this would lead nowhere.
precisely the point I was trying to make.
When my parents kicked me out, the number of times o got to sleep inside because i could convince people i was the county password inspector was more than zero. It’s hacking.
Wrench? No. But an old colleague informs me that the version done with a machete does count as hacking. I concur.
Those are both way more useful than exploiting a lazy coder’s fuckup, renaming ‘house of many backdoors’ to ‘that package everyone uses in everything’ on github, or some fancy math shit.
Your laws are nonsense bullshit, they’re just excuses for power and I’d appreciate you not defiling language fof the rest of us to justify them.
Those are both way more useful than exploiting a lazy coder’s fuckup
I never said social engineering, physical breaching, exerting force on people, and other ways of compromising systems weren’t useful. They just aren’t hacking to me, otherwise the term is too broad to be very useful.
You’re free to come up with your own definition, I was asked to define it and that’s my best shot for now.
I think a better definition would be “achieve something in an unintended or uncommon way”. Fits the bill on what generally passes in the tech community as a “hack” while also covering some normal life stuff.
Getting a cheaper flight booked by using a IP address assigned to a different geographical location? Sure I’d call that a life hack. Getting a cheaper flight by booking a late night, early morning flight? No, those are deliberately cheaper
Also re: your other comment about not making a reply at all, sometimes for people like us it’s just better to not get into internet fights over semantics (no matter how much fun they can be)
Your definition is probably better. I can very much vibe with that.
Mitnick mostly social engineered. Most of the big famous attacks at least involved a component of that.
Hacking isn’t hacking it’s usually cracking
Can be a component of it.
Mailing someone more letters than they’re capable of replying to is not equivalent to, nor a component of, gaining access to the inside of their home.
Disabling network security and edge devices to change the properties of ingress can absolutely be a component of an attack plan.
Just like overwhelming a postal sorting center could prevent a parcel containing updated documentation from reaching the receiver needing that information.
I haven’t heard of a firewall failing open when overwhelmed yet. Usually quite the opposite, a flood disables access to more than just the targeted device, when the state table overflows.
But maybe there is a different mechanism I’m not aware of. How would the DDoS change the properties of ingress?
By denying access to resources in a primary region, one might force traffic to an alternate infrastructure with a different configuration. Or maybe by overwhelming hosts that distribute BGP configurations. By denying access to resources, sometimes you can be routed to resources with different security postures or different monitoring and alerting, thus not raising alarms. But these are just contrived examples.
Compromising devices is a wide field with many different tools and ideas, some of which are a bit off the wall and nearly all unexpected, necessarily.
I mean, I know JK Rowling sucks, and it’s been a long time since the first Harry Potter movie came out, but it was definitely a component and precursor to Hagrid beating the shit out of that door.
To be fair, they had moved to an unsecure location that was a much softer target by that point. Can a DDOS force someone to move their services over to the equivalent of a century old, weather-beaten lighthouse in the middle of England?
Might be smart for Iran to just attack trump’s businesses as retribution for the bombings; if they attack the military, we’ll surely get pulled into another war, but just going after trump’s businesses will probably avoid a military response and maybe will make republicans come around to the fact that he should have divested himself from his businesses when he became president.
going after trump’s businesses will probably avoid a military response
More likely, it makes the poor baby (-hands) cry and throw a tantrum. Being the malignant narcissist he is, he thinks the resources of the United States government are entirely at his disposal. With that in mind, he’s absolutely going to demand a military response to any attacks on his businesses.
Whether saner heads prevail, all we can do is hope.
Yeah agreed, he’s absolutely going to demand a military response to any attacks on his business, but maybe that’s enough to divide the republicans in congress and they’ll start to rein him in. Still going to take a lot for them to develop the balls to stand up to him, but might be good for us if Iran just goes after his businesses.
Yeah these are the dicks that cried terrorism when Tesla was “attacked”
His administration says damage to Teslas equates to terrorism. I don’t think it would go how you’re thinking.
With any other president I’d agree but this is Trump. A venal and petty man who wouldn’t think twice before using the country’s soldiers and even nuclear weapons to defend his sense of pride
The bombings are an act of war, so Trump’s already dragged the US into a war with Iran at this point, despite the spin about being “at war with Iran’s nuclear programme but not Iran itself”
I doubt Iran are that worried about the Americans starting a ground invasion either, it would be an absolute bloodbath and will have MAGA and non-MAGA everywhere calling for Trump’s head.
Thankfully only DDos. Truth Social is Mastodon so a security flaw could have been a real problem.
nah it’s a lazy fork so seeing how he chooses people (they’re either cheap or friends of friends or both) “truth” can easily have a totally new security issue
maybe the server has a root password that’s “trump454748$$$”
Is It Mastodon?! For real? Does it have ActivityPub enabled and all of that?
It is a modified version of Mastodon, with a Soapbox front end. It does not have ActivityPub enabled and lacks a bunch of features.
The Mastodon developers then formally requested that Truth Social comply with the terms of the software license,[75] with Truth Social publishing its source code as a ZIP file on the website on November 12, 2021.
Lol they actually complied with the license in the end, i didnt know that.
Surely Trump could have ignored them, as an official act of course.
I wonder how much of it is vibe coded at this point…
This is the saddest good news I’ve ever read.
Never saw security flaw now as a real problem. You just have to live with the fact that there is one. And you will suffer when it’s used. Security flaw later is a real problem.
Do twitter next.
Fuck it, take down the entire internet
It’s been tried. A huge percentage of the internet runs on Amazon web services… And a massive ddos attack on that barely bumped it beyond the level of holiday shopping.
To get anywhere on “taking down the internet” they’d probably have to physically take out many sites across the globe.
“accidentally” leaving an anchor dragging across an intercontinental internet cable would do it
Russia is working on it just support Russia. /s
You say this like the hour all major SAAS went down 2 weeks ago was nothing. MILLIONS lost in business hours is not nothing.
Who gives a fuck about the travails of corporations on the internet?
The entire capitalist world only cares about that.
Feeling concern for the welfare of a corporation is a lot like caring for a lion or some other large predator. You don’t want to see it suffer but you know that it could turn on you at any moment, when it’s convenient for them.
Not even sure why/were you’re even taking this. They said a major outage was no worse than a website being overwhelmed by shoppers. I pointed out it’s in fact waaayyy worse. I don’t give a fuck about the corporations lost time.
Sea cables are probably the most vulnerable point of the internet. There are comparatively few of them (on the order of a few hundreds), they are long, and most of their length is not guarded at all. The only reason I can think of, why nobody has targeted them at large is that it would also cut of the attacker.
Iran pls hack Elon Musk’s Twitter account and post “I’m a mean old Nazi who sucks ass at Path of Exile 2”
Not just Elon’s account, shut the whole site down!
…we need a hack to prove that?
No, post an unhinged rant where he doesn’t say he’s a nazi, but he talks in detail about how he sucks at video games phrased as bragging, then shits on gamers for noticing, and says a buncha shit like the 14 words and junk.
Does that game have swords yet? Last time I played, not all classes were there.
Lol. Lmao, even
Thank you for your attention to this matter.
We have a president who issues fascistic edicts from the toilet and then phrases them like a Karen in her first term on her HOA or Condo board.
they have to start differentiating a ddos attack from an actual breach. one is far more interesting than the other
I work in tech and I hate it when non-security people talk about it.
It’s really painful to read about “a new hack that can affect billions of accounts” from a source, only to learn its some new social phishing method.
It seems like they just did us all a favor.
May just be the only thing that saves this country. Fewer people on social media is good for society at this point.
Is this how we find out that Truth Social was running even harder on hopes and dreams than 4chan was?